ActiveState Perl

Building with Containers?
Access a free low-to-no vulnerability container image for Perl.
Why ActiveState Perl?
ActiveState Perl is 100% compatible with community Perl, but is automatically built from vetted source code using a secure, SLSA-compliant build service in order to ensure its security and integrity. Secure your Perl software supply chain.
All stakeholders from security, compliance, and IT to developers, QA, and DevOps can centrally collaborate in order to facilitate curation, compliance, and consistency via policy for all Perl projects across the organization. Eliminate the risks inherent in managing Perl on a per project basis.
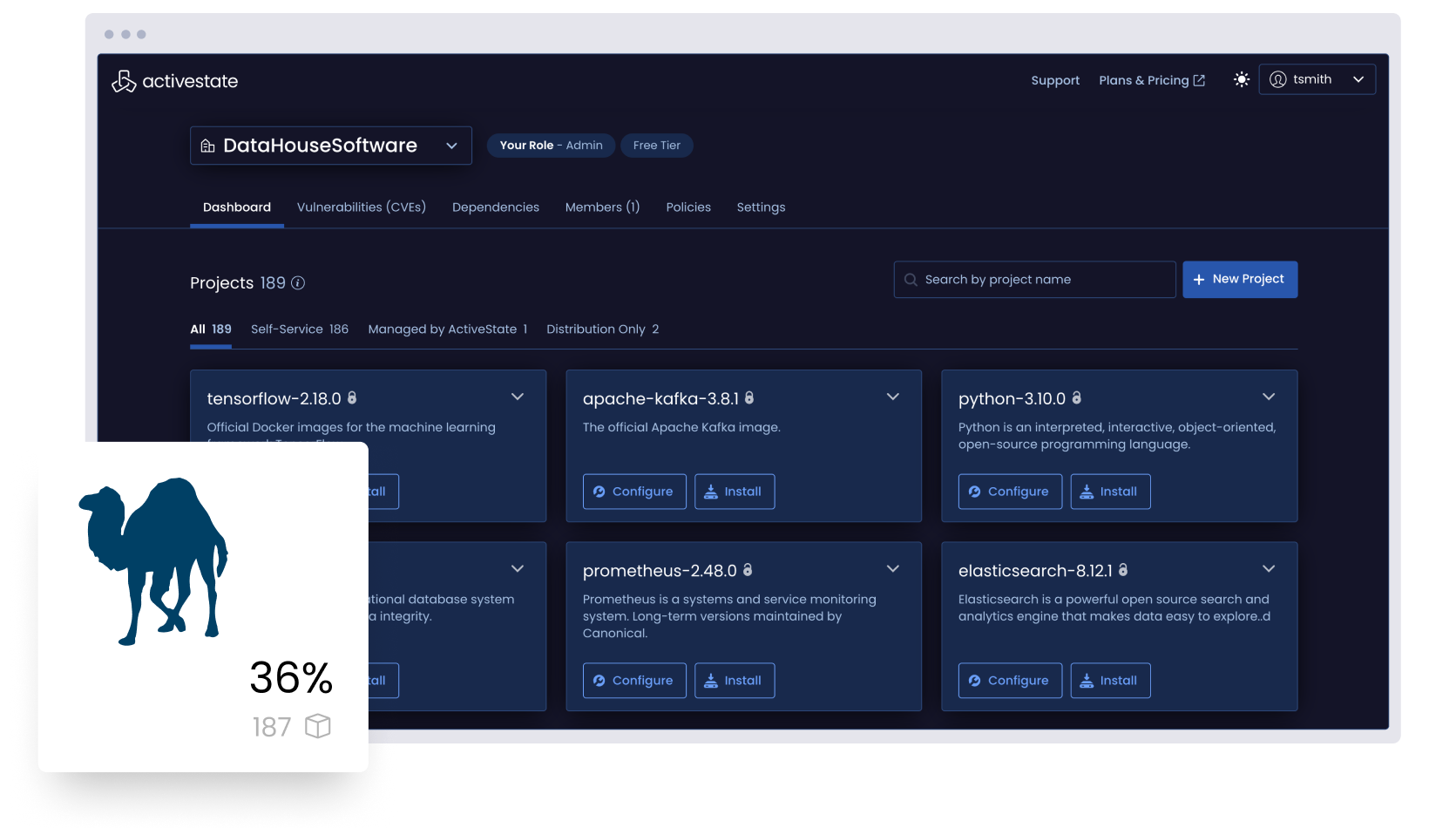
Manage all the Perl in your organization
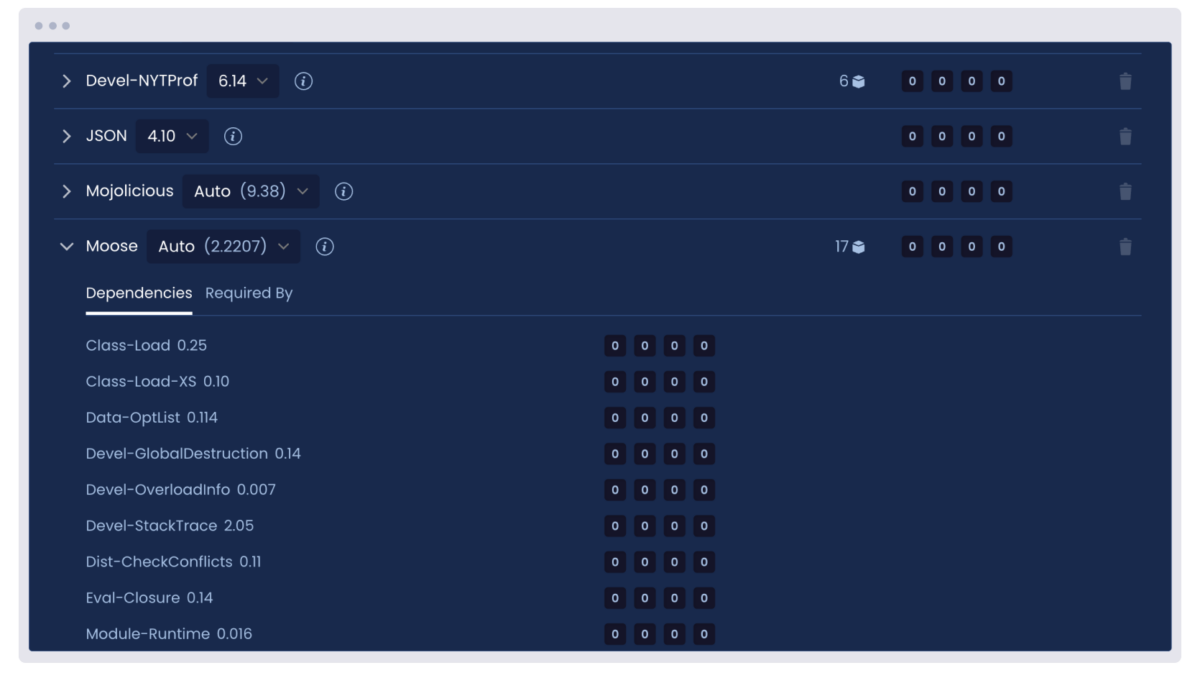
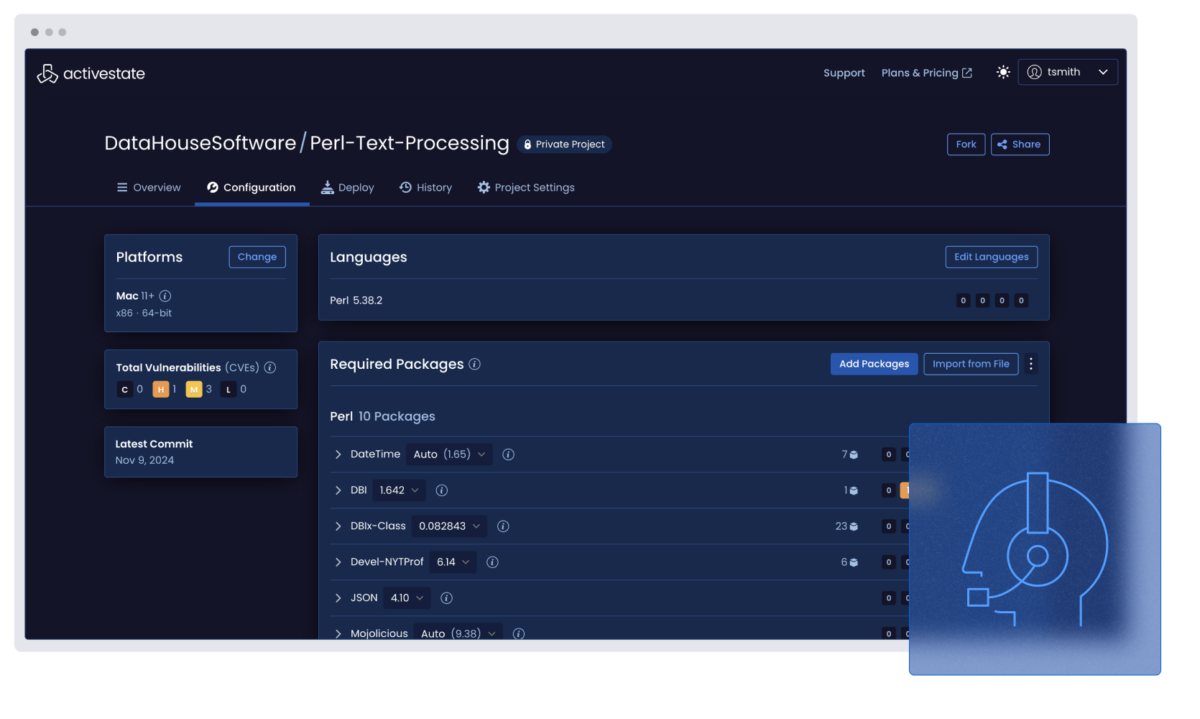
Visualize all the Perl deployed across your organization by top-level, transitive, and shared dependencies whether or not you use ActiveState Perl.
But for those looking to curate a catalog of securely built Perl artifacts, ActiveState Perl provides the ability to automatically build and centrally manage/deploy Perl runtimes in order to ensure consistency between environments for everyone from dev to test to CI/CD and production.
Analyze all the Perl deployed across your organization by license, vulnerability status, and more, whether or not you use ActiveState Perl.
Centrally collaborate with security, compliance, and IT personnel in order to implement a governance policy that can be applied to all Perl deployments. Flag policy violations, notify stakeholders, approve exceptions, and create an audit trail in order to ensure security and compliance with IT rules, industry guidelines, and government legislation.
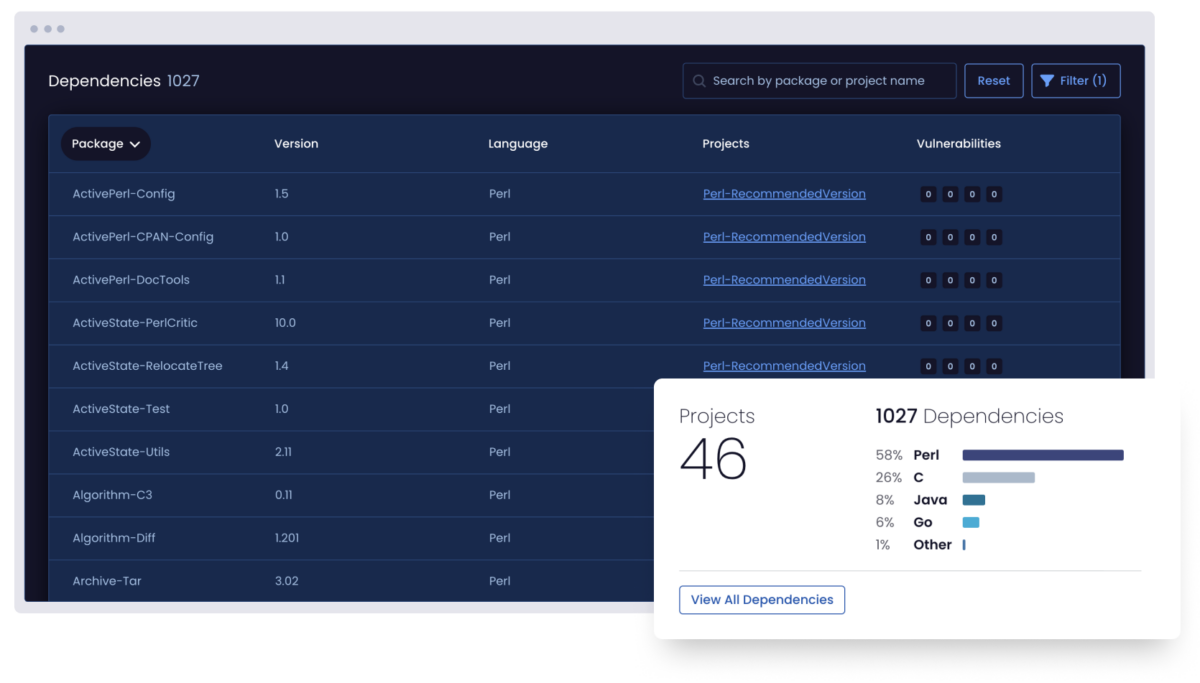
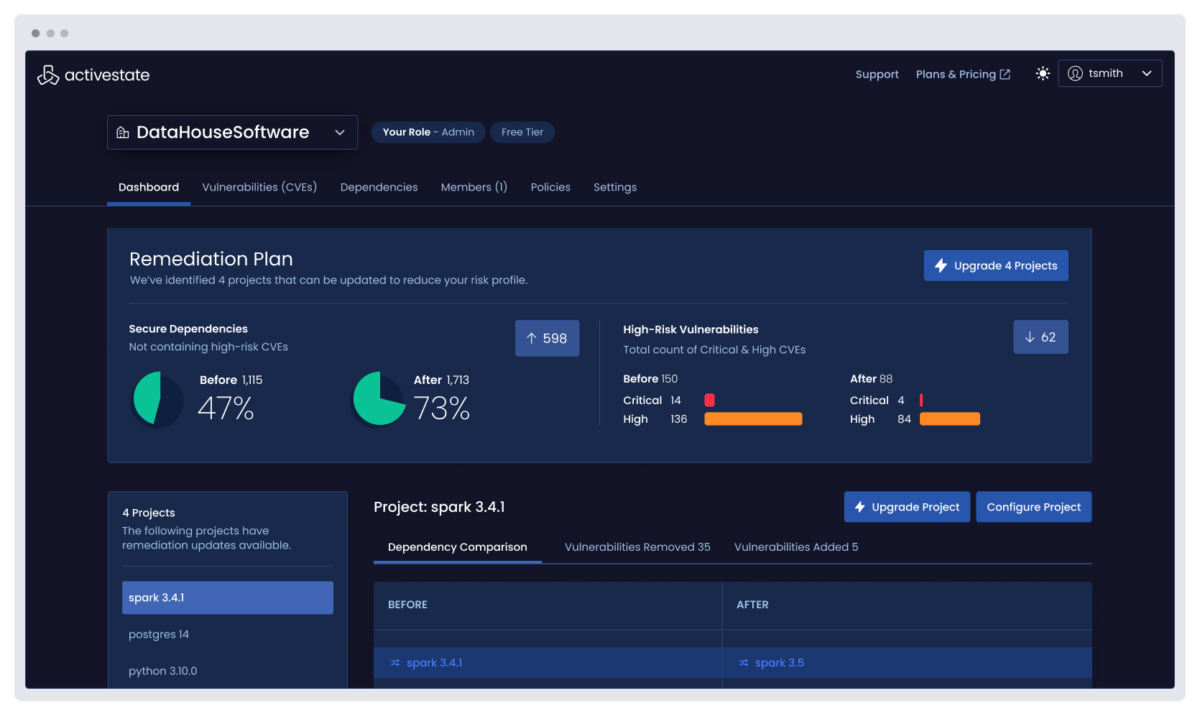
Remediate Perl vulnerabilities faster by centrally identifying all the vulnerabilities in every project across your enterprise, eliminating the threat of unidentified vulnerabilities and prioritizing remediation by understanding their impact.
Choosing to work with ActiveState Perl means you can also automatically rebuild runtime environments with fixed versions of vulnerable dependencies, reducing Mean Time To Remediation (MTTR).
Support the Perl you depend on for your commercial applications, even beyond EOL.
ActiveState provides long-term support for Perl deployments, ensuring you can continue to benefit from business-critical applications even after community support is no longer available. Let ActiveState backport security fixes so you can free up your team to focus on innovation.
Learn more about the benefits of working with ActiveState Perl
Perl Package Management Guide for Enterprise Developers
Developers that are willing to adopt the ActiveState Platform will spend less time wrestling with Perl package management tooling and more time focused on doing what they do best: coding.

Strawberry Perl Comparison
Gain more insight as to how ActiveState Perl differs from Strawberry Perl from both a development and security standpoint.

Perl Zero Day Security Threats
For Perl users that are worried about the security risks associated with running EOL versions of Perl, ActiveState is introducing an extended support offering that can help mitigate the risk.