The Next Attack Is Already In Your Pipeline.
In March 2026, TeamPCP stated they intend to continue their attack on open source Software. Get a free OSS Risk Assessment and find out whether your current open source posture is ready.
What the assessment looks like:
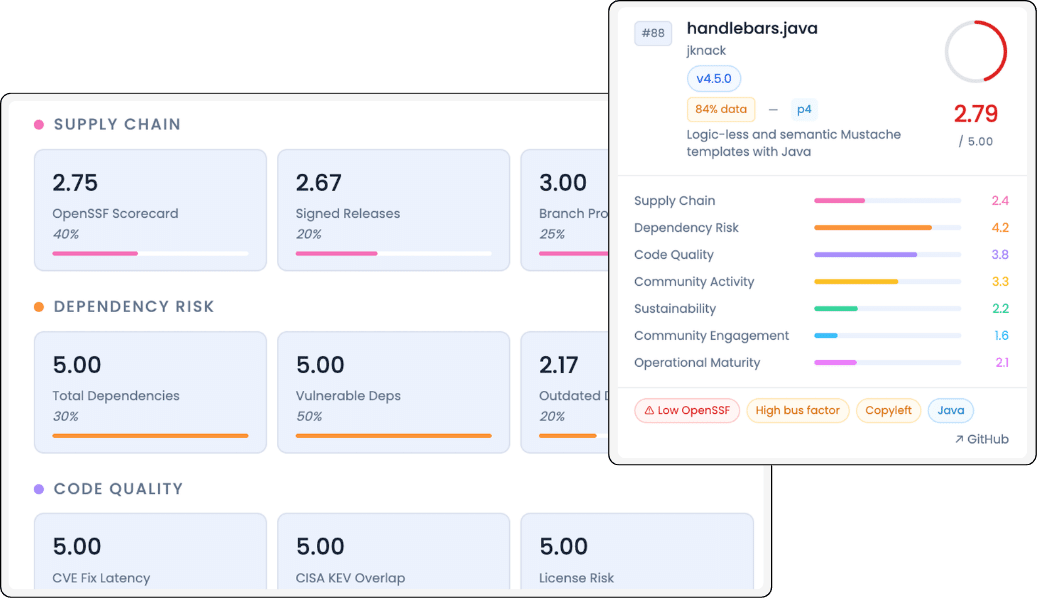
A personalized risk assessment — your ecosystem scored across eight dimensions using data from GitHub, OpenSSF, OSV.dev, CISA KEV, and deps.dev.
What your current tooling isn’t telling you:
- CVE count hides velocity: Two packages, same CVE count. One will be patched in 48 hours, the other has been open for 14 months. Most tooling treats them identically.
- Maintainer risk is untracked: A package whose sole maintainer hasn’t committed in eight months is one burnout away from abandonment. Most tooling does not surface this.
- License exposure is invisible: GPL and AGPL dependencies in production code create legal obligations most teams discover only after they become an issue.
- Upstream project health is invisible: Tooling doesn’t score the health of upstream projects that dependencies belong to: maintainer activity, organisational backing, release cadence.
- Release signatures are absent: Most open source releases carry no cryptographic signature. There is no way to verify the artifact you pulled was built by the maintainer and not tampered with in transit.
- Compliance evidence is retrospective: When a regulator asks for documented due diligence, a report showing open CVEs isn’t a solution.
How it works:
Intake call
We spend 30 minutes understanding your environment — what languages you are running, how your teams consume open source, and where your current governance gaps are. No slides. Just a direct conversation.
We do the work.
Our team runs an offline assessment of your open source software footprint. We’ll score popular open source packages across eight dimensions of risk, surfacing the structural vulnerabilities that software supply chain attacks are designed to exploit.
Outcomes and plan
We come back with what we found and a prioritized mitigation plan built for your environment. Not a generic framework. A specific plan your team can act on.
Ready to find out where your posture fails before an attacker does?
At ActiveState, we provide the only automated, built-from-source library of 79M secure components that plug right into your AI code generators and developer tools. We don’t just find the vulnerabilities—we’ve already remediated them at scale, so you can sign off on your software supply chain without putting your reputation on the line.