Resources
Featured content
- Blog
The Vulnerability Database Security Teams Depend On Just Hit a Structural Ceiling
NIST can no longer enrich all CVEs. If your security program depends on NVD data for prioritization, you now have a documented gap in your severity data. Here's what that means for your team.
Blog
The “As Is” Clause Was Never the Problem
The "as is" open source clause was never the problem — enterprise assumptions were. Discover why AI-assisted development has made legacy open source governance untenable, ...
Read More
New to ActiveState? Start here.
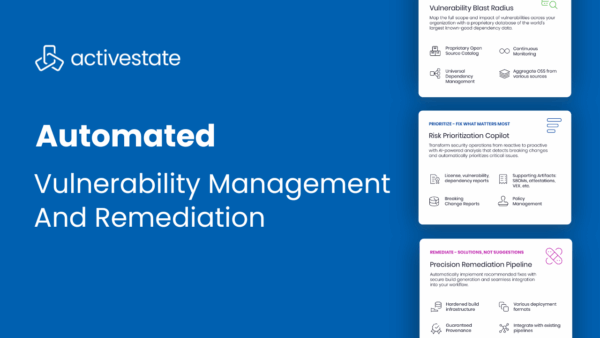
Automated Vulnerability Management & Remediation with ActiveState
May 1, 2025
Product Demo
ActiveState enables DevSecOps teams to not only identify vulnerabilities in open source packages, but also to automatically prioritize, remediate, and deploy fixes into production without ...
Read More
Top 3 Uses Cases for Managing Open Source at Scale
July 25, 2024
Blog
Managing open source complexities can slow down development. Point solutions only let you be reactive. Learn how to become proactive.
Read More
Tech Debt Best Practices: Minimizing Opportunity Cost & Security Risk
April 29, 2024
Whitepaper
Tech debt is an unavoidable consequence of modern application development, leading to security and performance concerns as older open-source codebases become more vulnerable and outdated. ...
Read More
Filters
- All
- Blog
- Case Study
- Data Sheet
- Product Demo
- Quick Read
- Video
- Webinar
- Whitepaper
All
- All
- Blog
- Case Study
- Data Sheet
- Product Demo
- Quick Read
- Video
- Webinar
- Whitepaper
The Vulnerability Database Security Teams Depend On Just Hit a Structural Ceiling
May 6, 2026
Blog
NIST can no longer enrich all CVEs. If your security program depends on NVD data for prioritization, you now have a documented gap in your ...
Read More
Global Proprietary Trading Firm Hardens Python Supply Chain against Malicious Attacks with ActiveState
May 5, 2026
Case Study
Python security for financial firms starts with eliminating public repository risk. See how a global trading firm moved to a private, source-built catalog with ActiveState ...
Read More
The “As Is” Clause Was Never the Problem
May 5, 2026
Blog
The "as is" open source clause was never the problem — enterprise assumptions were. Discover why AI-assisted development has made legacy open source governance untenable, ...
Read More
When “Secure by Default” Only Works in One Tool, You Don’t Have a Governance Model
April 30, 2026
Blog
AI coding assistants are making dependency decisions faster than your team can review them. A tool-level integration only governs the developers who use that tool. ...
Read More
15 Container Security Best Practices for Engineering Teams in 2026
April 27, 2026
Blog
Learn 15 container security best practices for engineering teams, including Kubernetes policies, secrets management, and runtime protection.
Read More
The Quiet Foundation of AI-Native Development
April 24, 2026
Blog
AI agents are resolving open source dependencies at machine speed, with no human in the loop. ActiveState gives your environment the provenance, remediation, and reproducibility ...
Read More
Your Open Source Governance Program Is Already Behind. Here’s How Far.
April 23, 2026
Blog
Most open source software security failures aren't caused by a lack of tooling — they're caused by governance programs that haven't kept pace with how ...
Read More
IDC Analyst Brief | Securing Open Source at Scale: How Consumption Complexity Creates Supply Chain Risk
April 23, 2026
Resources
ActiveState has sponsored an IDC Analyst Brief to examine why open source software governance is failing at scale, and what security leaders need to do ...
Read More
JFrog Curation and ActiveState Curated Catalog Are Not the Same Thing
April 21, 2026
Blog
Stop the confusion between JFrog Curation and ActiveState Curated Catalog. Learn how these two distinct security layers—policy at the distribution point and source-level verification—work together ...
Read More
Operationalizing SBOMs: From SPDX and CycloneDX to OpenVEX and Provenance
April 16, 2026
Blog
Learn how to operationalize SBOMs using SPDX, CycloneDX, OpenVEX, and provenance to improve your organization’s vulnerability posture.
Read More
Project Glasswing: Is Your Remediation Infrastructure Ready?
April 14, 2026
Blog
96% of applications contain open source components. Most of the vulnerabilities in those components are about to be found. That’s not hyperbole. It’s the rational ...
Read More
Navigating the Labyrinth: Mastering Java Dependency Management with ActiveState
April 7, 2026
Blog
Master Java dependency management with ActiveState. Move beyond Maven and Gradle to achieve environment hermeticity, proactive conflict resolution, and end-to-end security.
Read More