Resources
Featured content
- Blog
The Quiet Foundation of AI-Native Development
Master Java dependency management with ActiveState. Move beyond Maven and Gradle to achieve environment hermeticity, proactive conflict resolution, and end-to-end security.
Blog
The Quiet Foundation of AI-Native Development
Master Java dependency management with ActiveState. Move beyond Maven and Gradle to achieve environment hermeticity, proactive conflict resolution, and end-to-end security.
Read More
New to ActiveState? Start here.
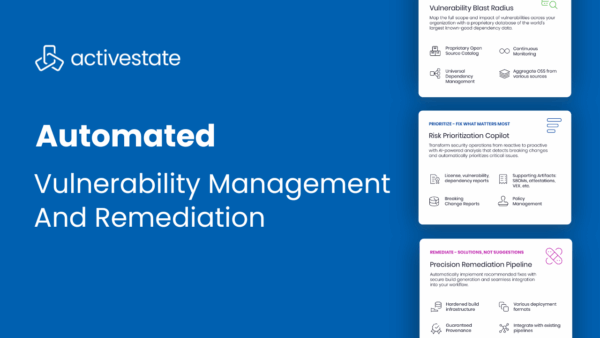
Automated Vulnerability Management & Remediation with ActiveState
May 1, 2025
Product Demo
ActiveState enables DevSecOps teams to not only identify vulnerabilities in open source packages, but also to automatically prioritize, remediate, and deploy fixes into production without ...
Read More
Top 3 Uses Cases for Managing Open Source at Scale
July 25, 2024
Blog
Managing open source complexities can slow down development. Point solutions only let you be reactive. Learn how to become proactive.
Read More
Tech Debt Best Practices: Minimizing Opportunity Cost & Security Risk
April 29, 2024
Whitepaper
Tech debt is an unavoidable consequence of modern application development, leading to security and performance concerns as older open-source codebases become more vulnerable and outdated. ...
Read More
Filters
- All
- Blog
- Case Study
- Data Sheet
- Product Demo
- Quick Read
- Video
- Webinar
- Whitepaper
All
- All
- Blog
- Case Study
- Data Sheet
- Product Demo
- Quick Read
- Video
- Webinar
- Whitepaper
The Quiet Foundation of AI-Native Development
April 24, 2026
Blog
Master Java dependency management with ActiveState. Move beyond Maven and Gradle to achieve environment hermeticity, proactive conflict resolution, and end-to-end security.
Read More
Your Open Source Governance Program Is Already Behind. Here’s How Far.
April 23, 2026
Blog
Most open source software security failures aren't caused by a lack of tooling — they're caused by governance programs that haven't kept pace with how ...
Read More
IDC Analyst Brief | Securing Open Source at Scale: How Consumption Complexity Creates Supply Chain Risk
April 23, 2026
Resources
ActiveState has sponsored an IDC Analyst Brief to examine why open source software governance is failing at scale, and what security leaders need to do ...
Read More
JFrog Curation and ActiveState Curated Catalog Are Not the Same Thing
April 21, 2026
Blog
Master Java dependency management with ActiveState. Move beyond Maven and Gradle to achieve environment hermeticity, proactive conflict resolution, and end-to-end security.
Read More
Operationalizing SBOMs: From SPDX and CycloneDX to OpenVEX and Provenance
April 16, 2026
Blog
Learn how to operationalize SBOMs using SPDX, CycloneDX, OpenVEX, and provenance to improve your organization’s vulnerability posture.
Read More
Project Glasswing: Is Your Remediation Infrastructure Ready?
April 14, 2026
Blog
96% of applications contain open source components. Most of the vulnerabilities in those components are about to be found. That’s not hyperbole. It’s the rational ...
Read More
Navigating the Labyrinth: Mastering Java Dependency Management with ActiveState
April 7, 2026
Blog
Master Java dependency management with ActiveState. Move beyond Maven and Gradle to achieve environment hermeticity, proactive conflict resolution, and end-to-end security.
Read More
Container Security Tools: How to Choose the Right Solution at Each Stage of the Container Lifecycle
April 2, 2026
Blog
Container hardening reduces risk at build time, but not after deployment. Learn how to secure the full software lifecycle.
Read More
If You Use axios, Stop What You’re Doing
March 31, 2026
Blog
Learn how to detect and remediate zero-day vulnerabilities across the software lifecycle and reduce exposure before disclosure.
Read More
What the RSAC™ 2026 Conference Told ActiveState About the State of Security — And Where We Go From Here
March 31, 2026
Blog
Every year, RSAC brings the security industry together — and every year, the conversations on the floor reveal where the real pressure points are. In ...
Read More
Container Hardening Is Only Step One: How to Secure the Full Software Lifecycle
March 26, 2026
Blog
Container hardening reduces risk at build time, but not after deployment. Learn how to secure the full software lifecycle.
Read More
Open Source Is Under Attack. Here’s How to Manage the Risk Without Abandoning the Benefit
March 25, 2026
Blog
In March 2026, a threat actor known as TeamPCP executed one of the most consequential open source supply chain attacks on record. Starting with a ...
Read More