ActiveState Library
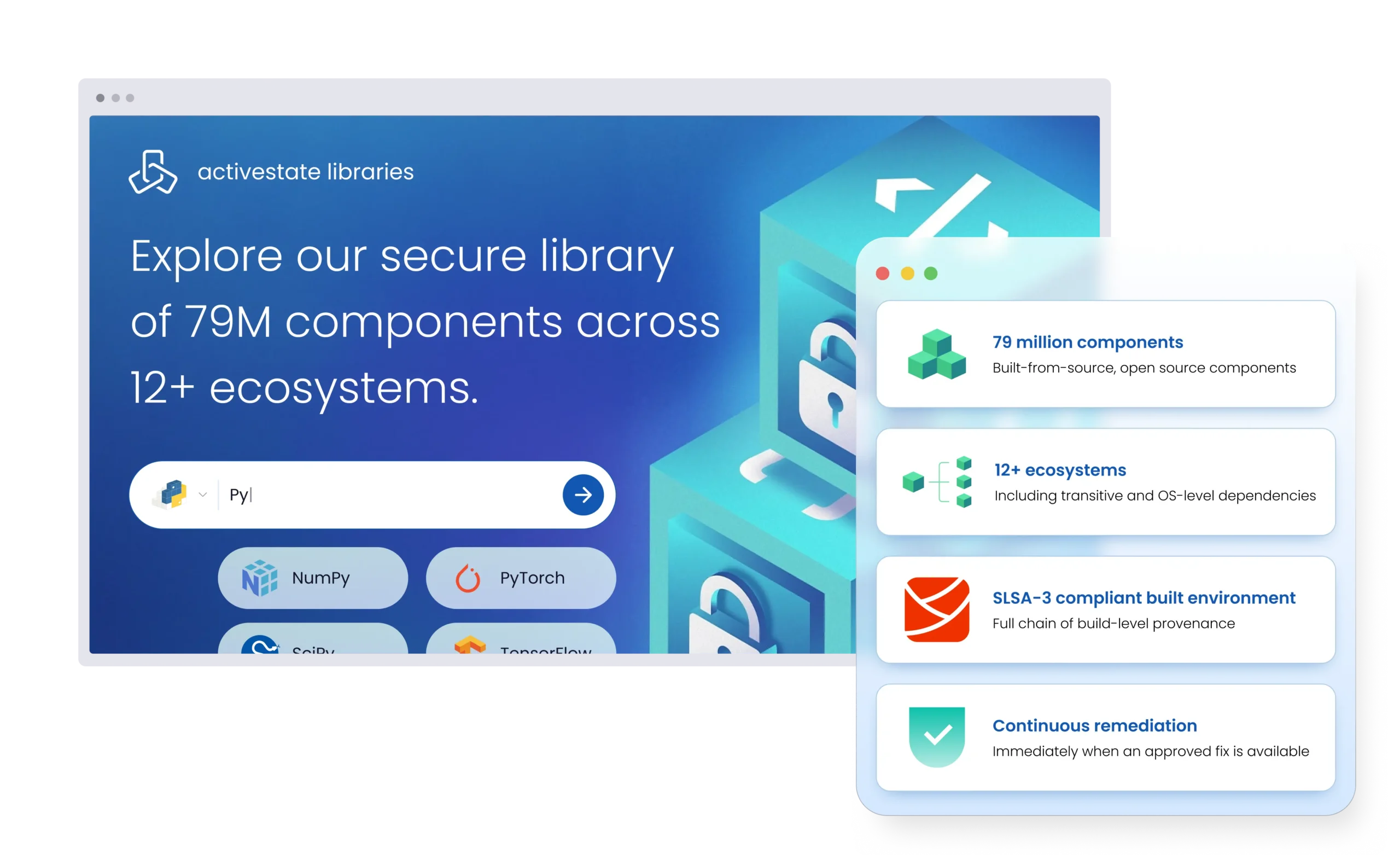
The world’s largest catalog of secure, trusted, and continually remediated open source available in three consumption models.
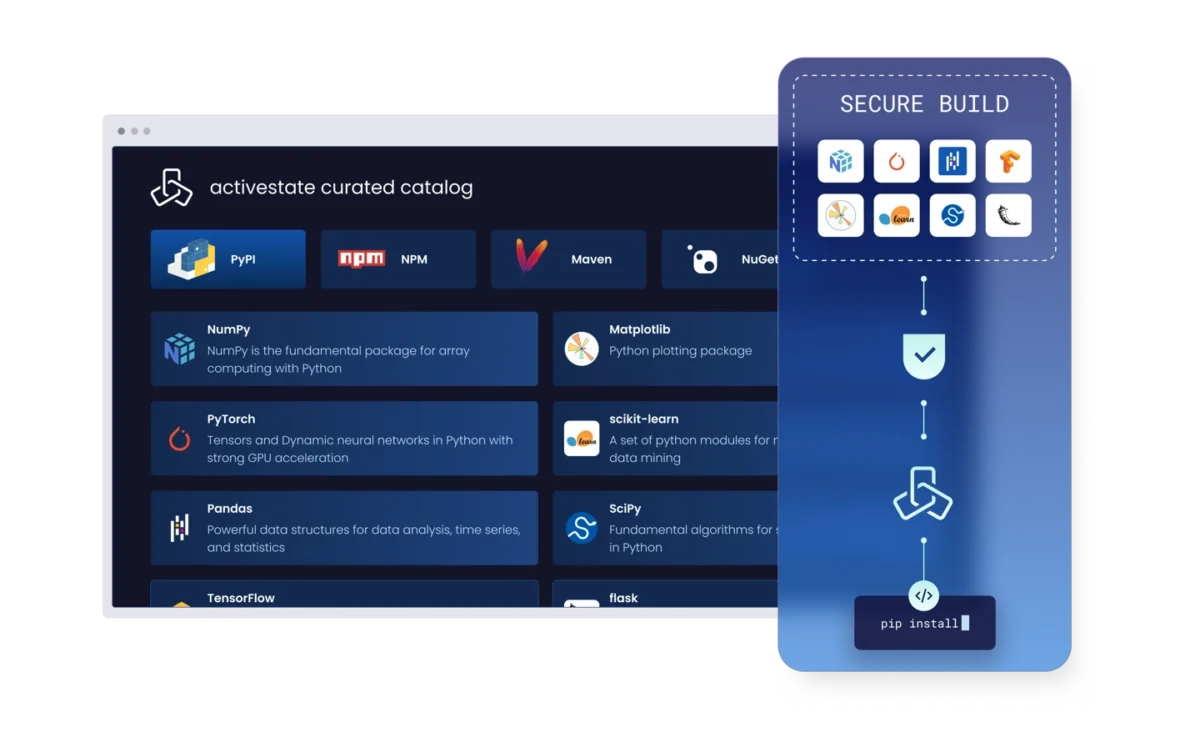
ActiveState Curated Catalog
Curate a private and vetted repository of open source components from the ActiveState Library that developers can use safely without having to scour the open internet. A Curated Catalog provides security teams total control over what comes into their environments while giving engineering teams a fast and secure way to get what they need to build, onboard, and start new projects.
Key Features:
- Direct access to selected components and their dependencies leveraging your own internal repository such as JFrog Artifactory, Sonatype Nexus, etc.
- Component remediation when fixes are available upstream
- Point to ecosystem tooling, such as pip, to provide native access within your CI/CD pipelines
- Consume using leading artifact repository tools
- Security feed for component level vulnerabilities
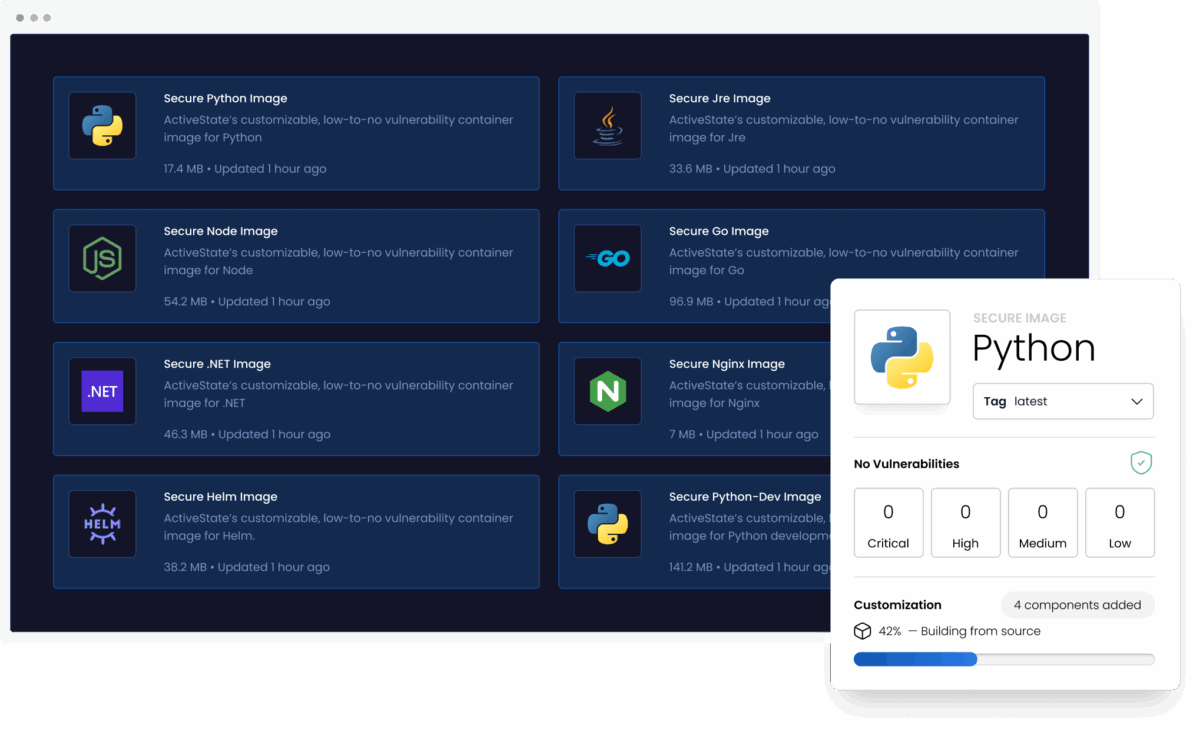
ActiveState Secure Containers
Build and deploy with confidence using base or fully customizable, low-to-no CVE container images for popular languages and open source applications. Container images are fully managed and remediated by ActiveState.
Key Features:
- Access minimal, hardened images for popular languages and apps built from source
- Base images are fully customizable using the ActiveState Library
- All images are rebuilt regularly
- Images are maintained according to our SLA (5 business days for critical CVEs, 10 for high, and 30 days for all others)
- All images ship with full build-time provenance including signatures and SBOMs
ActiveState Managed Distributions
Build and deploy with confidence using fully reproducible custom language runtimes for any operating system. Runtimes are fully managed and remediated by ActiveState.
Key Features:
- Fully reproducible language runtimes for any operating system
- Customize runtimes using pre-vetted components from the ActiveState Library
- Runtime builds and dependencies are fully handled by ActiveSate
- Apply component-level fixes when available
- All runtimes ship with full build-time provenance
FAQs
How can we guarantee that only vetted, secure open source packages are used by our developers?
Malware and CVEs are stopped at the source, reducing the amount of risk teams must manage. Built from source components guarantee dependency compatibility across environments.
- 100% protection from compromised package ecosystems and build systems
- Mitigate high-profile malware attacks such as the npm Shai-Hulud attack and other future threats
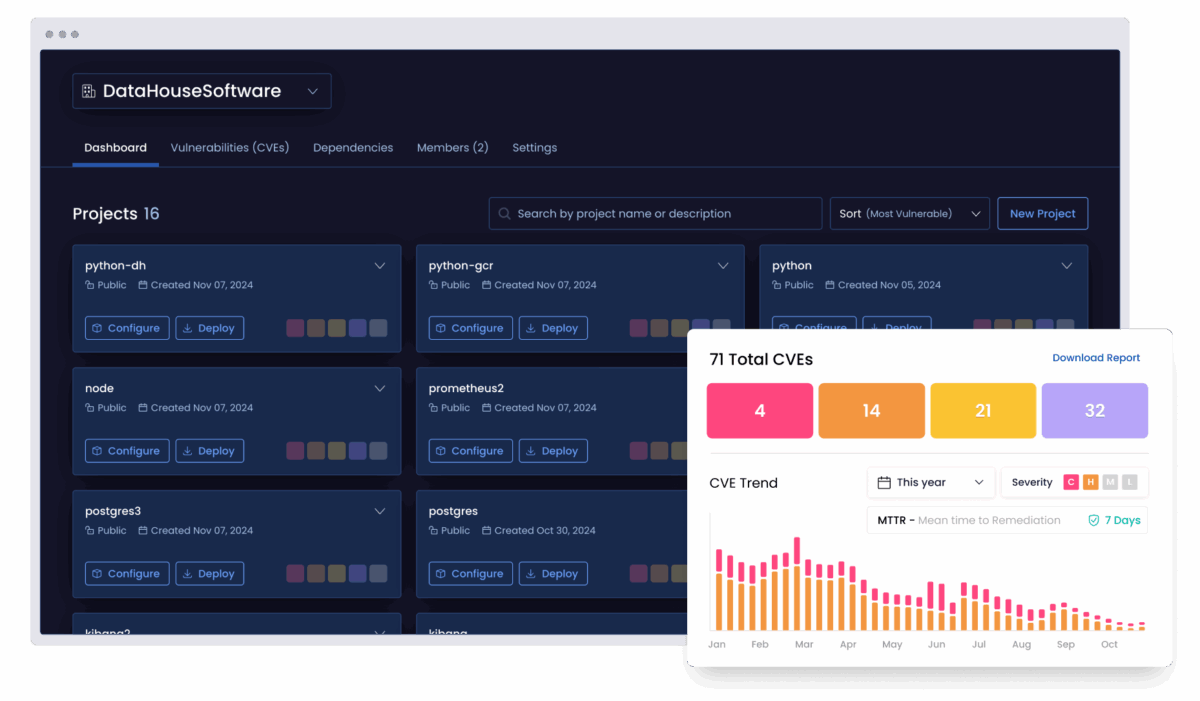
How can we ensure that our open source inventory remains secure against emerging threats?
CVEs are continually identified, triaged, and remediated by ActiveState.
- Up to 99% reduction in CVEs compared to community open source artifacts
- Achieve up to ~90% reduction in MTTR for future vulnerabilities
- 68% reduction in scanner noise from false positives
How can we move from manual security gates to automated guardrails within our existing CI/CD pipeline?
The optimal way is to ensure seamless integration of security policy into existing tooling and workflows. This helps you shorten open source approval workflows from weeks and days to hours and minutes.
How can we eliminate the manual effort required to audit our open source inventory?
End-to-end visibility across open source usage and easy access to supporting metadata and documentation helps eliminate manual efforts. Achieve 100% visibility into your open source usage including transitive and OS-level dependencies using ActiveState.
What is the solution for engineering teams struggling with the manual burden of vulnerability management?
With ActiveState managing the ongoing security of your open source, vulnerability triage and remediation work is offloaded from engineering teams to our team. Dependency management is handled by the ActiveState build engine. This means you can:
- Free up 4-8 developer hours per CVE
- Reduce scanner noise from false positives by 68%



