Resources
Featured content
- Blog
The Vulnerability Database Security Teams Depend On Just Hit a Structural Ceiling
NIST can no longer enrich all CVEs. If your security program depends on NVD data for prioritization, you now have a documented gap in your severity data. Here's what that means for your team.
Blog
The “As Is” Clause Was Never the Problem
The "as is" open source clause was never the problem — enterprise assumptions were. Discover why AI-assisted development has made legacy open source governance untenable, ...
Read More
New to ActiveState? Start here.
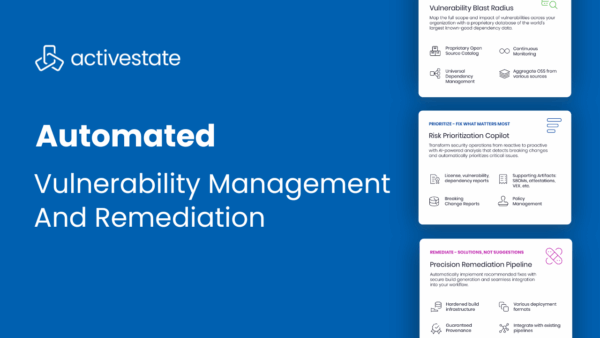
Automated Vulnerability Management & Remediation with ActiveState
May 1, 2025
Product Demo
ActiveState enables DevSecOps teams to not only identify vulnerabilities in open source packages, but also to automatically prioritize, remediate, and deploy fixes into production without ...
Read More
Top 3 Uses Cases for Managing Open Source at Scale
July 25, 2024
Blog
Managing open source complexities can slow down development. Point solutions only let you be reactive. Learn how to become proactive.
Read More
Tech Debt Best Practices: Minimizing Opportunity Cost & Security Risk
April 29, 2024
Whitepaper
Tech debt is an unavoidable consequence of modern application development, leading to security and performance concerns as older open-source codebases become more vulnerable and outdated. ...
Read More
Filters
Sorry, we couldn't find any posts. Please try a different search.