ActiveState Secure Containers




Container security without compromise.
Why choose between container security and developer flexibility when you can have both? Choose from our catalog of minimal, low-to-no CVE images or customize one to your exact needs.
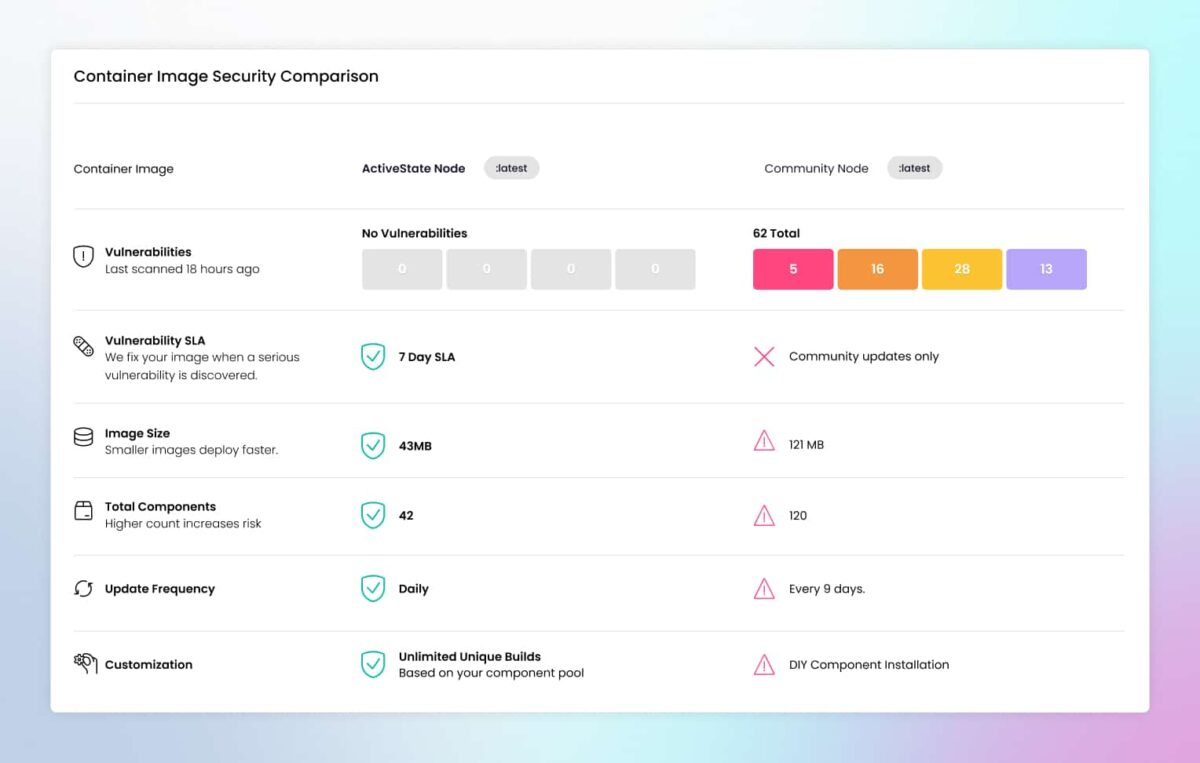
- Strengthen your security posture: Achieve up to 99% fewer CVEs than community images while still leveraging the open-source functionality you need.
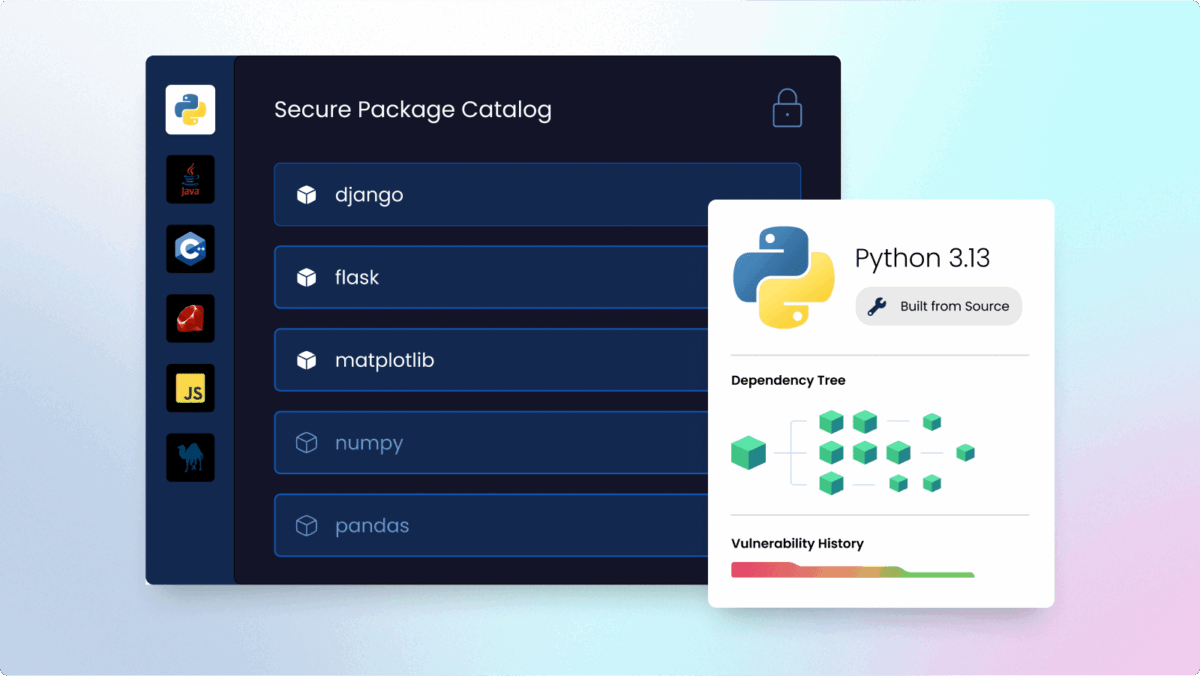
- Lock down your supply chain: Customize container images using over 40M secure, source-rebuilt components. Add trusted packages, additional configurations, or secure language language libraries.
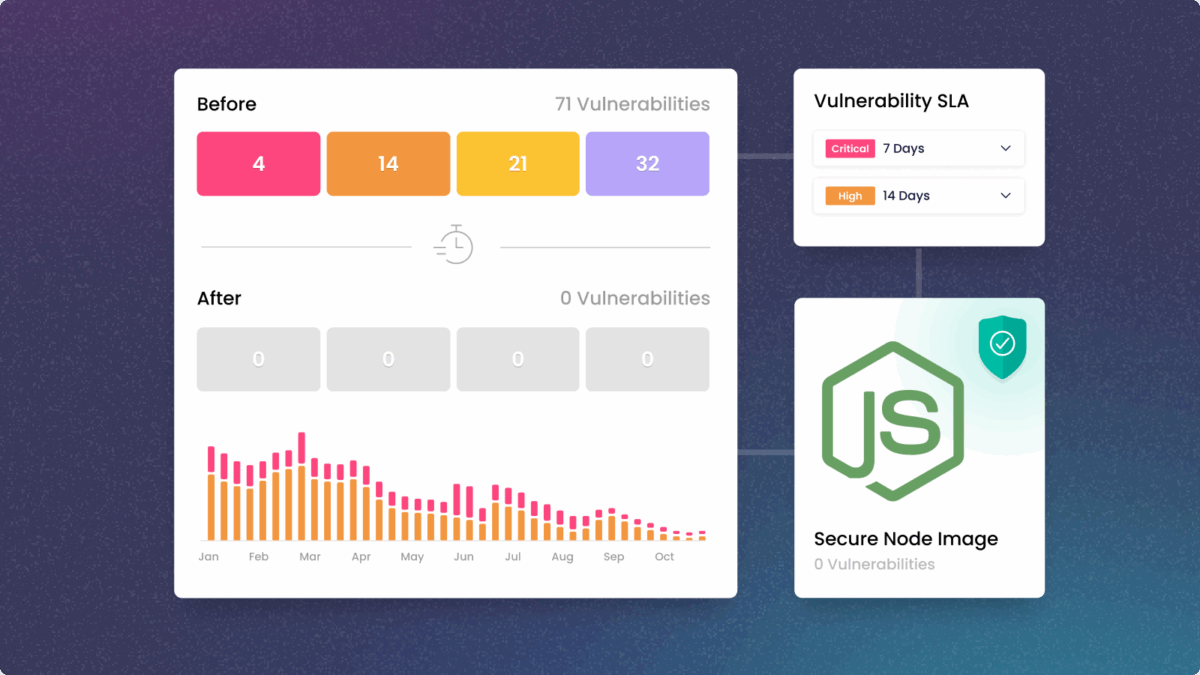
- Reduce engineering toil: Future CVEs? Not to worry, automated component-level remediation applies patches everywhere they’re needed — freeing developers to focus on features, not CVEs.
- Simplify compliance: Meet complex standards faster with complete build-time SBOMs, and optional customization for FIPS or STIG hardening.
“I don’t have to think too much about security and the complications anymore because ActiveState does it for me.”
– Stacy Leon, Sr. Technical Specialist
Fully secure. Fully customizable.
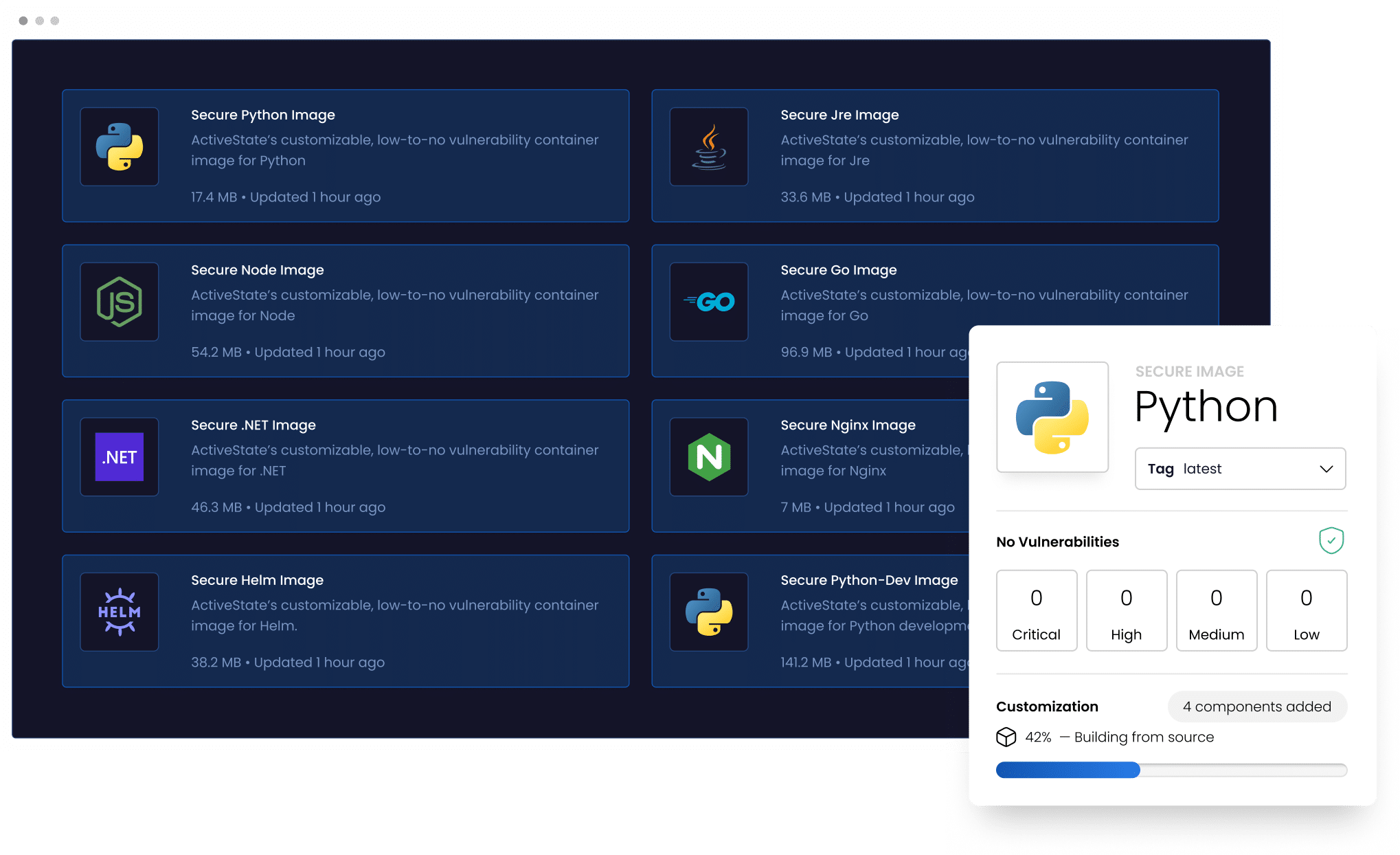
Secure containers for development and deployment
Pull from our growing library of minimal, secure container images. Each image includes a complete SBOM and is rebuilt nightly to ensure you are always up to date.
Customize without compromise
Customize or build any image using over 40M secure, source-rebuilt components. Add packages, configurations, secure language libraries or optional compliance requirements.
New CVE discovered? We've got you
All base and custom images are automatically remediated at a component level and rebuilt according to our leading remediation SLA of 7 days for critical and high CVEs.
Get started with ActiveState Secure Containers
Whether you need something from our catalog, want to customize an existing image, or require something built from scratch—we’ve got you covered:
- Request a custom build
- Add packages, configurations, or secure language libraries
- Access specific tags and image variants
- Meet compliance requirements (FIPS, STIG, and more)
FAQs
What makes ActiveState Secure Containers more secure than standard images?
Unlike typical container images, ActiveState containers use a custom distroless base (containing only essential dependencies with no shell, package manager, or debugging tools), build all components from source rather than using pre-compiled binaries, and undergo nightly rebuilds with strict remediation SLAs to maintain near-zero vulnerabilities.
Are free container images available?
Yes, the latest versions of ActiveState Secure Containers are available for free via our catalog . These include popular programming languages for deployment, developer variants, and useful applications.
Can I customize ActiveState images to fit my specific needs?
Yes, ActiveState offers a fully managed container build service using their catalog of over 40 million secure open-source components. Custom images can include specific configurations, additional packages, or language libraries tailored to your exact requirements.
What are the remediation SLAs for vulnerabilities?
ActiveState maintains industry-leading remediation SLAs of 7 days for critical and high CVEs, and 14 days for all other vulnerabilities. All images are rebuilt nightly and automatically remediated when vulnerabilities are detected.
Do ActiveState images support compliance requirements?
ActiveState containers are built with compliance in mind, providing complete visibility and traceability through detailed buildtime SBOMs (Software Bills of Materials), cryptographic signatures for image verification, and comprehensive VEX advisories for all identified vulnerabilities. In addition, all images can be customized to include further hardening (i.e., FIPs, STIG).
Explore more resources
10 Container Security Best Practices Every Engineering Team Should Know
Containers have become the gold standard for building modern, cloud-based software. It’s no surprise – using containers for app development has plenty of benefits.

Hardened Container Security Best Practices
It’s no secret that containers enable you to deploy products rapidly in scalable and consistent environments, however they also can introduce new vulnerabilities across the software supply chain. In this whitepaper, we explore common container security challenges and best practices to overcome them.

Chainguard vs ActiveState Hardened Containers
Learn how you can decrease Mean Time To Remediation (MTTR) by outsourcing the responsibility of securing your containers to a third party.




