Open source speeds up development but introduces risks
The open-source community revolutionized software development, driving the speed of innovation and collaboration across the globe. With the increased reliance on open-source components, over 80% of software projects are comprised of Open Source, and the risk posed by a vulnerable OSS dependency has grown significantly.
Using a security dashboard for vulnerability management
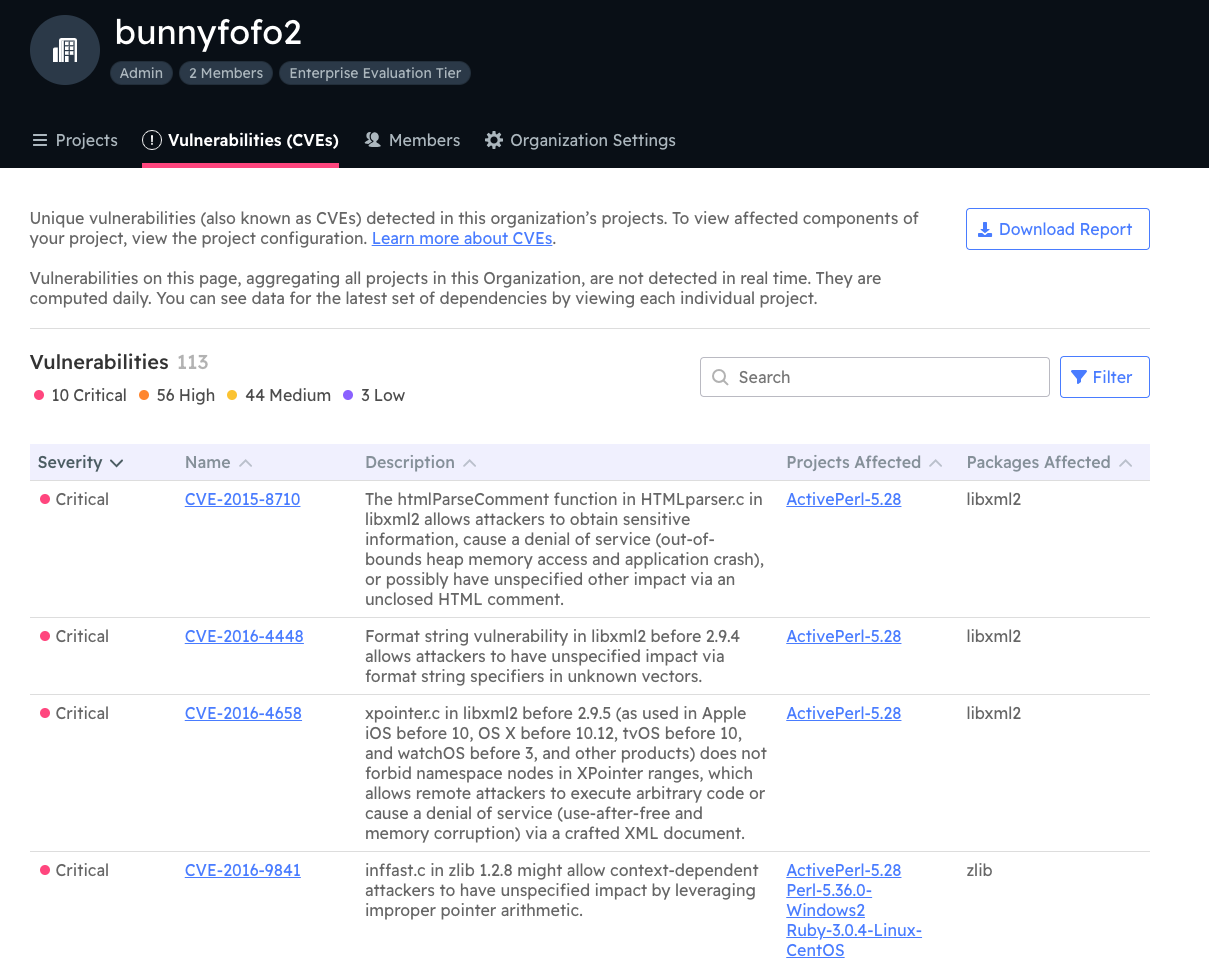
The use of open-source components brings immense benefits, but it also introduces supply chain risks. Vulnerabilities discovered in one Open Source project can potentially affect other projects, proprietary and open source, that use the same component. Our Security Dashboard helps show you risks of different severity contained within all your projects using open source dependencies provided by ActiveState. This is similar to what many Software Composition Analysis tools do, but at ActiveState we vendor dependencies we have built from code so we are in a position to identify risks that may be hidden deeper than just those identified by using only your requirements file.
Previously in the ActiveState Platform you could only see your project’s vulnerabilities when viewing that project, and could only pull a report for that one project.
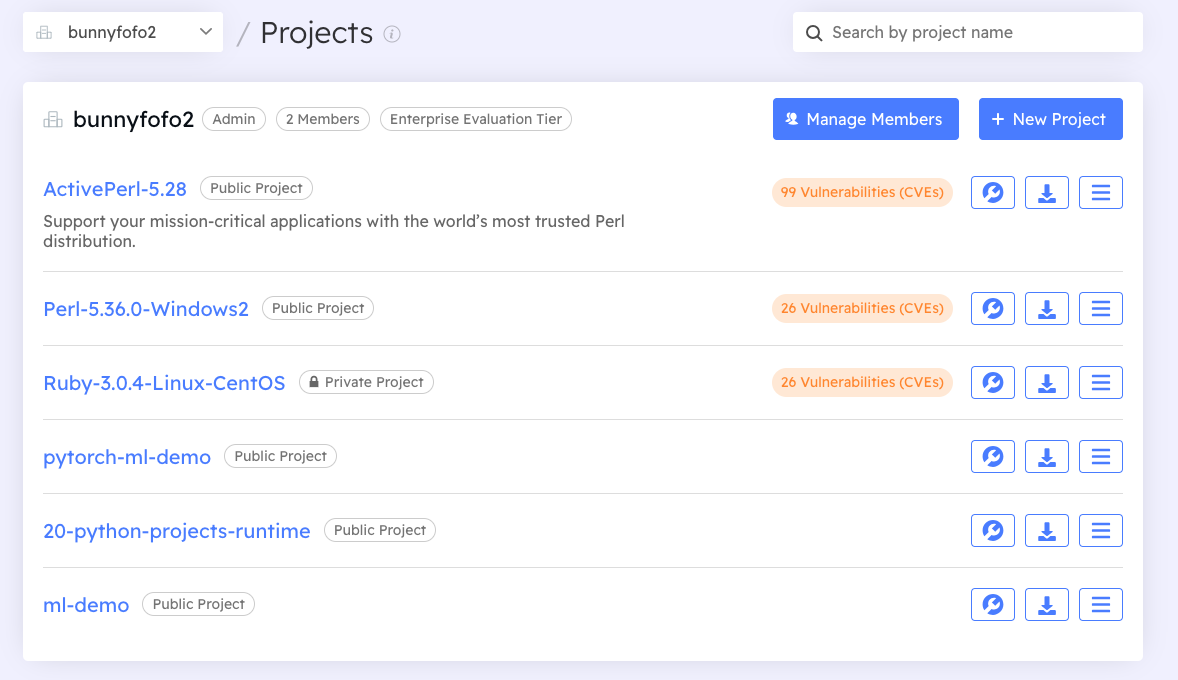
To make managing your vulnerabilities easier for both security teams and developers, we’ve added an Organizational Security Dashboard which aggregates the vulnerability information across all your ActiveState projects, which also allows you to download as a CSV report.
 We have also added summary information on the project list.
We have also added summary information on the project list.
Security teams often need to monitor a wide range of software and platforms to identify potential threats. This centralized oversight saves time and effort, allowing developers and security teams to focus on remediation and risk mitigation. This aggregation enables security teams to obtain a comprehensive view of existing vulnerabilities across different projects, regardless of their size or complexity.
The benefits of a security dashboard
For organizations subject to regulatory requirements or compliance standards, an aggregated vulnerability dashboard proves invaluable. It simplifies the process of auditing and reporting vulnerabilities across open-source projects, ensuring that the organization maintains a secure and compliant software ecosystem.
As open-source components continue to power the software development landscape, mitigating potential vulnerabilities becomes a paramount concern. The Open Source Vulnerability Dashboard, offering an aggregate of vulnerabilities across multiple projects, proves to be an invaluable tool for developers and security teams alike. By consolidating vulnerability data, organizations can enhance awareness, strengthen proactive security measures, facilitate risk assessments, foster collaboration, streamline patch management, and drive continuous improvement.
Implement the ActiveState security dashboard in your dev process today
We originally introduced this feature based on customer requests. We have many ideas of how to iteratively improve it, but we want to hear from you!
To get access to this feature for free through October 1st, sign up here in exchange for access we will ask you to provide feedback on the feature (what enhancements you want to see, what you liked, what you did not like, etc!)
Next steps:
Sign-up to access the security dashboard feature for free until October 1st. You can also get a demo from an ActiveState expert to demonstrate how to use the dashboard as well as other ActiveState Platform features.
Read Similar Stories

Learn how you can take your existing systems and convert them to SLSA-ready implementations in order to help secure your supply chain.
Read how you can use the ActiveState Platform to secure your builds and as a result secure the weakest link in your software supply chain.
Get a 5 minute overview of the security dashboard.








