Enterprise-Wide Vulnerability Dashboard
Learn how the ActiveState Vulnerability Dashboard is designed to do just that by providing a comprehensive view of dependencies and their vulnerabilities, enabling more effective risk assessment and remediation effort.
Software developers have long deployed tools and processes to ensure they have visibility into the open source dependencies they use. Unfortunately, too many organizations track only top-level packages, and may not have visibility into the complete list of transitive dependencies those packages are pulling in.
Additionally, enterprises may have visibility on a per business unit basis, but lack an automated way to determine organization-wide risk posed by a vulnerability, making prioritization and triage more difficult.
It’s these kinds of blind spots that generate unnecessary risk, and can only be overcome by implementing a vulnerability dashboard that eliminates silos and identifies vulnerabilities across the extended enterprise, down to the lowest-level transitive dependency.
Open Source Observability
Open source observability starts with a comprehensive catalog of all dependencies, transitive dependencies and shared libraries for all software assets, no matter where they’re deployed across the extended enterprise.
But with organizations increasing their use of open source components, the number of vulnerabilities being reported has exploded, resulting in ever-escalating risk due to:
- Hackers exploiting economies of scale: a single compromised open source package incorporated into a popular software application can allow them to potentially hack thousands of customers.
- 80% of codebases never being updated for fear of breaking the build, which leads to applications riddled with open source vulnerabilities.
These trends are exacerbated by silos, whereby:
- Each project may have different methods of obtaining the open source resources they require, including risky processes like downloading prebuilt, unsigned packages or source code from public repositories.
- Even when all open source artifacts are built from source code, they may be built on an unsecured developer desktop rather than a hardened build service.
- Open source components may be deployed on a project to project basis from a variety of prebuilt distributions that quickly become out of date.
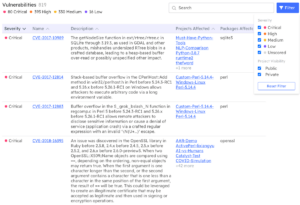
ActiveState CVE Dashboard
Open source observability is key to breaking down silos and reducing security risk, which means all stakeholders need to be able to visualize:
- The complete list of dependencies in use across the organization, including all transitive dependencies, shared libraries and OS-native binaries.
- Where each set of dependencies is deployed across the extended enterprise.
The ActiveState Vulnerability Dashboard is designed to do just that by providing a comprehensive view of dependencies and their vulnerabilities, enabling more effective risk assessment and remediation efforts.
It also allows security teams to regain control over proliferating projects and the open source dependencies they include by providing a single, central view of all open source runtime environments created for use:
- Visualize the security status of every project
- Filter by severity
- Search for specific CVEs
- At-a-glance view of number of affected projects, facilitating triage
- Comprehensive list of affected dependencies, including all transitive dependencies