Resources
Featured content
- Blog
From Vulnerable to Unbreakable: The Evolution of Container Security in Modern Software Development
New to ActiveState? Start here.
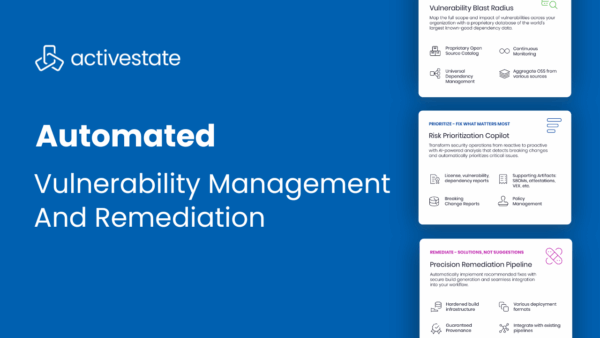
Automated Vulnerability Management & Remediation with ActiveState
May 1, 2025
Product Demo
ActiveState enables DevSecOps teams to not only identify vulnerabilities in open source packages, but also to automatically prioritize, remediate, and deploy fixes into production without ...
Read More
Top 3 Uses Cases for Managing Open Source at Scale
July 25, 2024
Blog
Managing open source complexities can slow down development. Point solutions only let you be reactive. Learn how to become proactive.
Read More
Tech Debt Best Practices: Minimizing Opportunity Cost & Security Risk
April 29, 2024
Whitepaper
Tech debt is an unavoidable consequence of modern application development, leading to security and performance concerns as older open-source codebases become more vulnerable and outdated. ...
Read More
Filters
- All
- Blog
- Case Study
- Data Sheet
- Product Demo
- Quick Read
- Video
- Webinar
- Whitepaper
All
- All
- Blog
- Case Study
- Data Sheet
- Product Demo
- Quick Read
- Video
- Webinar
- Whitepaper
Infographic: Tame the Complexity of Open Source Across your Organizations
September 13, 2024
Data Sheet
ActiveState provides a unified platform to discover, manage, and secure your open source software across multiple ecosystems and deployment environments, fostering collaboration between development, security, ...
Read More
Unlocking $8.8T of Secure Open Source Software
September 11, 2024
Blog
To take advantage of $8.8T of OSS effectively requires putting in place governance: the policies & processes that help manage & control risks.
Read More
How US Government ISVs Can Quickly Verify CISA Attestation
August 29, 2024
Whitepaper
Software companies that sell to the US government face new hurdles when it comes to getting or keeping lucrative US government contracts: the need to ...
Read More
Supply Chain Security for FinServ
August 28, 2024
Blog
FinServ treats software supply chain security like reactive cybersecurity, making more work for AppSec. Learn how to be proactive instead.
Read More
How to Tame The Complexity of Open Source Dependency Security
August 22, 2024
Blog
Outsourcing DepSec to a trusted partner can close the gap in securing your open source supply chain without overburdening your AppSec team.
Read More
Top 5 AI CyberSecurity Risks For Finserv
August 16, 2024
Blog
With the GenAI revolution sweeping FinServ, cybersecurity threats continue to grow. Learn how you can address the top 5 risks posed by GenAI.
Read More
Software Supply Chain Security for Cloud Apps
August 8, 2024
Blog
Creating secure, container-based Cloud apps requires a secure software supply chain for both containers & their contents. Learn your options.
Read More
The Open Source Security Gap
August 1, 2024
Blog
Most ISVs rely on a binary repository to warn them whether the open source they’ve already imported poses a risk, which is too often too ...
Read More
Top 3 Uses Cases for Managing Open Source at Scale
July 25, 2024
Blog
Managing open source complexities can slow down development. Point solutions only let you be reactive. Learn how to become proactive.
Read More
Adopting SSDF: US Government Best Practices for Securing Your Software Supply Chain
July 22, 2024
Webinar
Governments are introducing new regulations for fighting software supply chain attacks. Are you prepared? Learn how to adopt secure software development practices to keep your ...
Read More
DepSec: How DevOps Can Secure Open Source at Scale
July 19, 2024
Blog
Automating dependency security is key to allowing DevOps to manage the observability, compliance and remediation of open source at scale.
Read More
How US Government ISVs Can Meet CISA Attestation Requirements
July 11, 2024
Blog
ActiveState can help bridge the gap between your current capabilities & CISA Attestation requirements via a single easy-to-integrate platform
Read More