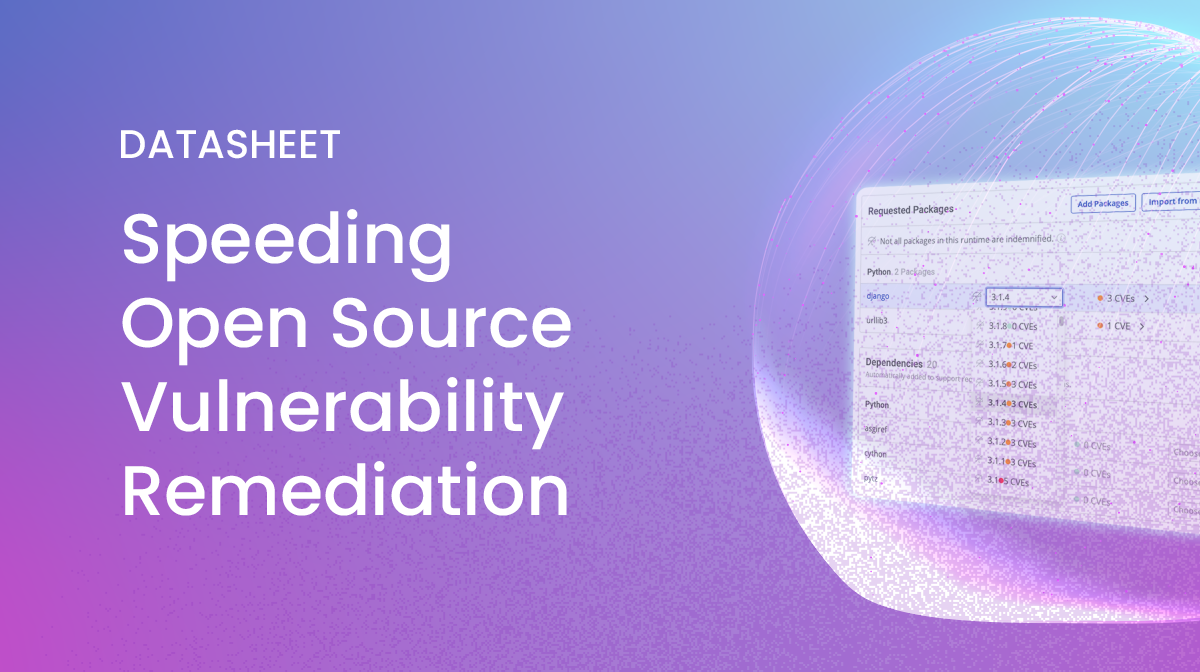
The CVEs published by the US National Vulnerability Database (NVD) continue to grow from decade to decade. It’s simply becoming harder and harder for developers to keep up. And of course, attackers only need one unpatched vulnerability to exploit, while defenders need to patch everything. This data sheet explains how you can use the ActiveState Platform to dramatically shorten the time to remediate vulnerabilities, ensuring the security of your open source supply chain.
Figure 1: Time to patch vulnerabilities
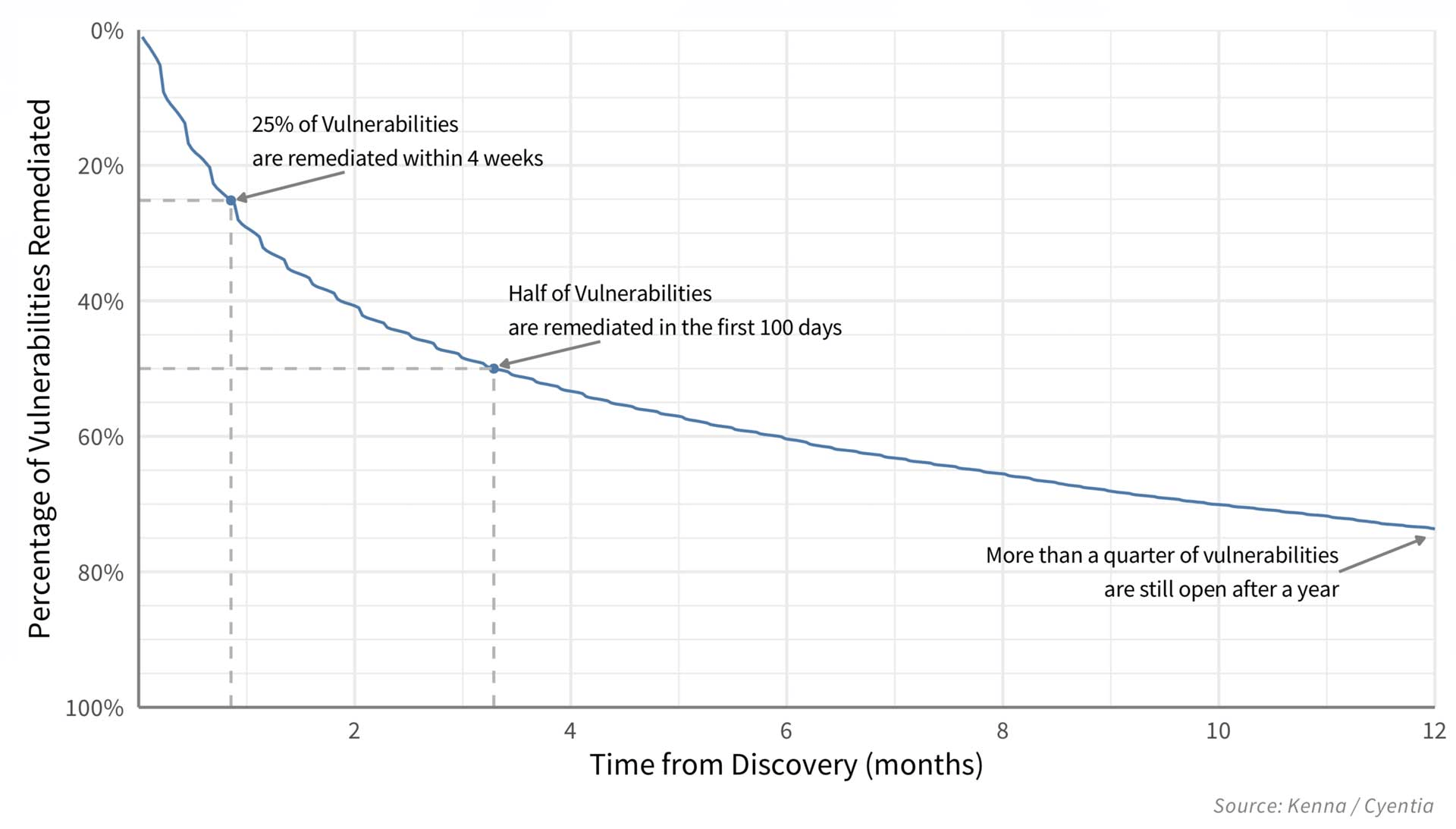
Resolve Open Source Vulnerabilities Faster
The ActiveState Platform is a universal package management solution for Python, Perl and Tcl that can help you secure your open source supply chain.
Two of the most important issues faced by development teams include timely vulnerability remediation and knowing which component/version of a component is safe to use. The ActiveState Platform addresses both issues, while ensuring that managers can meet key metrics like Mean Time To Detection (MTTD) of vulnerabilities and Mean Time To Remediation (MTTR) for your applications.
- Reduce MTTD – you can’t secure vulnerabilities you don’t know about, which is why the ActiveState Platform provides:
- A detailed Bill of Materials (BOM) for each of your Python, Perl and Tcl projects, showing exactly which components are currently vulnerable.
- A vulnerability status that shows the number of vulnerabilities by severity level for each of your projects, allowing you to identify risk.
- A PDF report that provides details on each vulnerability, and which you can email to all stakeholders increasing awareness.
- Reduce MTTR – rather than waiting for a patch to be released, the ActiveState Platform uniquely lets you take action right away by:
- Indicating which version(s) of a component are vulnerable and which aren’t, enabling a quick upgrade/downgrade as opposed to a lengthy investigation.
- Showing the ramifications of choosing a specific version of a component on the rest of your environment BEFORE you commit to it, ensuring you’re always using secure, compatible components.
- Automatically rebuilding your environment for Windows and Linux in minutes, ready for deployment, dramatically reducing the build-and-test cycle.
About ActiveState
ActiveState is the de-facto standard for millions of developers around the world who have been using our commercially-backed, secure open source language distributions for over 20 years. With the ActiveState Platform, developers can now automatically build their own Python, Perl or Tcl Environments for Windows, Linux or Mac—all without requiring language or operating system expertise.
How to try the ActiveState Platform for your Python, Perl and Tcl projects?
Developers can sign up for our Platform and use it to build a runtime environment for their Python projects right away. Or they can install it via the command line using the snippet provided here.
Up to 5 Active Runtimes per organization (or per individual, if for personal use) are free. For information on team tier or enterprise pricing, refer to our Platform Pricing or contact Sales.
Your software supply chain is only as secure as its weakest link. Book a demo and let us show you how the ActiveState Platform can secure it from end-to-end.