How to use the ActiveState Platform for generating SBOMs (Software Bill of Materials)
This video provides a quick overview of how the ActiveState Platform can be used to generate an SBOM for all the open-source language components in your software project. You can do so by simply querying the ActiveState Platform’s GraphQL API. Follow along step by step and give it a try for your own projects.
To create your own runtime environment, featuring up-to-date, secure packages and their fully resolved dependencies, you can start by creating a free ActiveState Platform account.
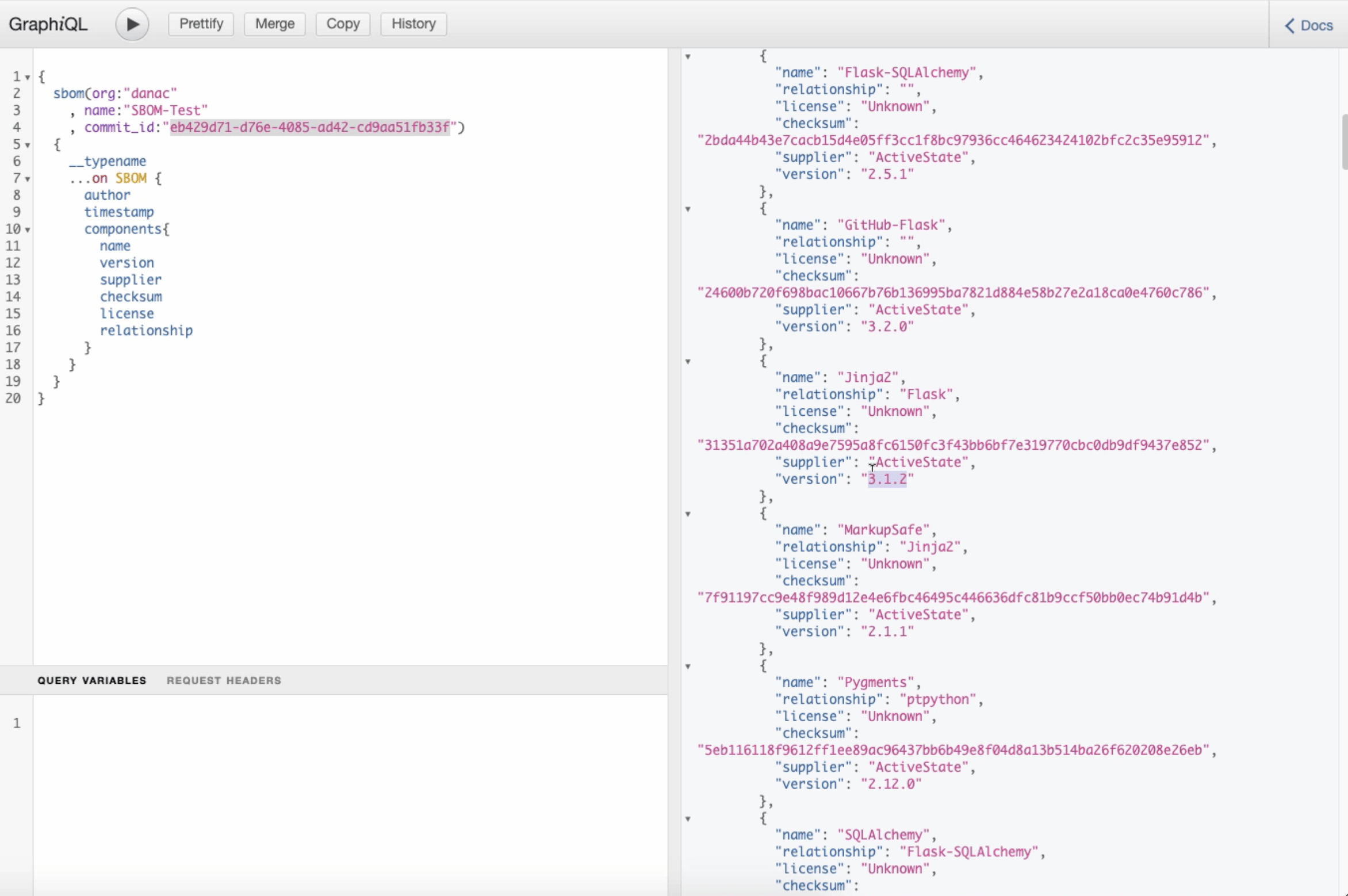
The ActiveState Platform’s GraphQL API provides programmatic access to detailed information about the runtime environment for your software applications. If you have a configuration file for your Python, Perl, or Ruby application, you can simply:
- Create a runtime environment on demand in just a few minutes.
- Use the GraphQL API to generate an SBOM for that runtime, which shows:
- Supplier – the name of the software vendor/author
- Version – the published version of the component
- Name – the name of the component
- Relationship – which component is dependent upon other component(s)
- License – the high-level license of the component
This feature allows customers to understand and identify all the components in their runtime environments (packages, libraries, dependencies, etc.) to allow security and compliance personnel to track and audit the software, and satisfy their cybersecurity, legal, and compliance requirements. Reports are generated in either a lightweight JSON or a signed heavier-weight ISO Standard SPDX v2.2.1 format.
 Note: Creating secure, reproducible environments are functions available to all users of the ActiveState Platform, including free-tier users. Just start by creating your account using your email or GitHub credentials. As you work with the ActiveState Platform to create new Python environments, you may need to upgrade to higher tiers to obtain access to features available only to paid-tier users. These include role-based access control and project branching. Please get in touch with us to help you find the best tier for your needs.
Note: Creating secure, reproducible environments are functions available to all users of the ActiveState Platform, including free-tier users. Just start by creating your account using your email or GitHub credentials. As you work with the ActiveState Platform to create new Python environments, you may need to upgrade to higher tiers to obtain access to features available only to paid-tier users. These include role-based access control and project branching. Please get in touch with us to help you find the best tier for your needs.
Watch Next: How to Use the ActiveState Platform for Modern Open Source Package Management
At ActiveState, we use the Platform to build not only our popular open-source language distributions but also custom runtimes for our enterprise clients (i.e., builds containing just the language and packages their project requires). Try it out yourself or get a personalized demo and understand how it can support your enterprise’s open-source needs.
To read the blog based on this video “How Software Bill of Materials (SBOMs) Support Secure Development,” head here.







